Table of Contents
ToggleProtect Your Organisation: Top Cybersecurity Risks – Prepare, Respond or React?
Where Expertise Meets Impact:
A Joint Article by CLA Global TS and CLA Global Indus Value Consulting
Cybersecurity is a critical component for all organisations and businesses, involving the use of technologies, processes, and practices to protect sensitive information from malicious threats and unauthorised access.
Why does Cybersecurity Matter to Businesses?
Regardless of the scale of the corporation, cybersecurity is crucial to the safety of the organisation, and the consequences of a breach increase as the company grows.
1. Small and Medium Enterprises (SMEs)
SMEs are often seen as easier targets due to the lack of sophisticated security measures. A singular cyberattack could result in financial loss, reputational damage and even business closure.
2. Large Corporations
Stakes are higher for larger corporations. Massive data breaches, regulatory penalties and loss of customer trust can all be results of a cyberattack.
Cybersecurity Landscapes – Regulatory Frameworks
To counteract and enforce security against malicious cyberattacks, comprehensive evaluation of all the potential and known cyber threats that exist must be thoroughly investigated. The findings lay the groundwork for establishing the Regulatory Frameworks that are now implemented:
1. Cybersecurity Act 2018
The Act establishes a legal framework for the oversight and maintenance of national cybersecurity in Singapore.
2. Personal Data Protection Act (PDPA)
Baseline standard of protection for personal data in Singapore. It comprises various requirements governing the collection, use, disclosure and care of personal data in Singapore.
3. MAS Technology Risk Management (TRM) Guidelines
Applies to financial institutions, outlining the minimum cybersecurity standards and best practices.
4. Computer Misuse Act
Designed to prevent unauthorized access to computer systems, cyber extortion, and other forms of computer misuse.
5. Sector-specific Cybersecurity Guidelines
- Infocomm Media Development
- Authority Ministry of Health
6. ISO 27001 – The Information
Structured framework to safeguard their information assets and information management security systems, covering risk assessment, risk management and continuous improvement.
Top Cybersecurity Risks in 2024-2025
Over the years many types of cyberattacks have made headlines. Analysing the threat and the frequency of such cyberattacks, it has been found that the top cybersecurity risks in 2024-2025 are:
- Ransomware
- Phishing Attacks
- Insider Threats
- Advanced Persistent Threat
- Supply Chain
- Cloud Security
- DDOS
- Social Engineering Attack
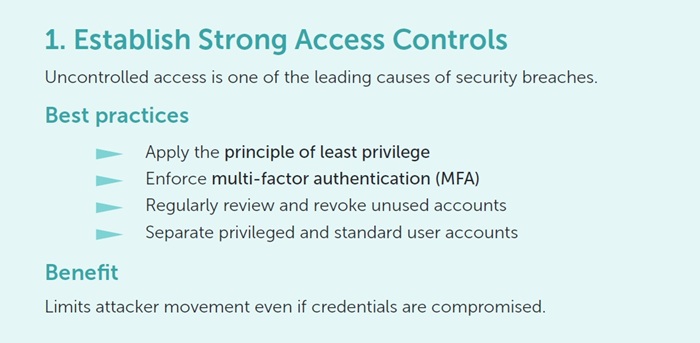
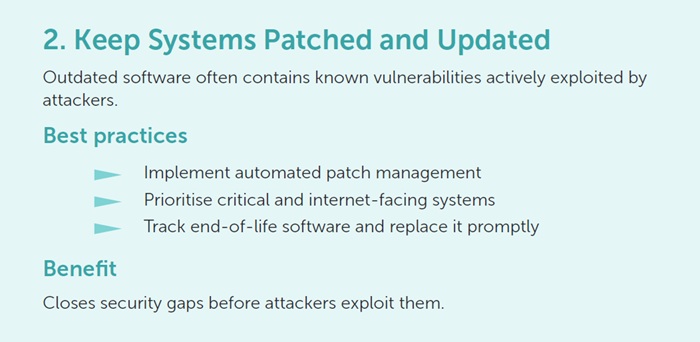
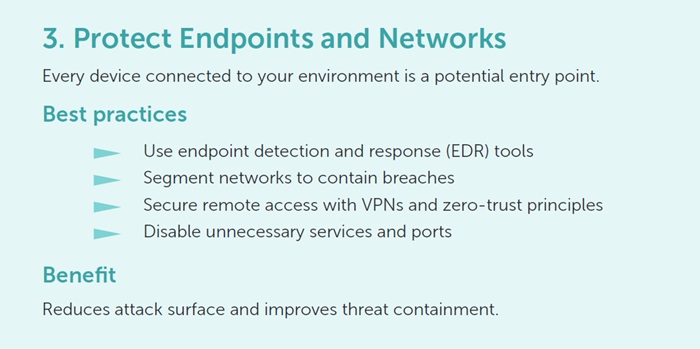
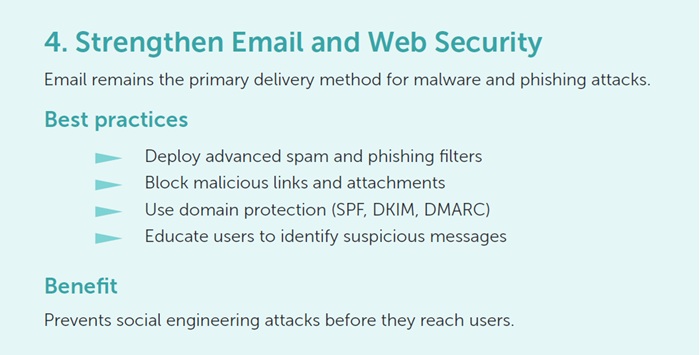
Best Practices for Securing Systems
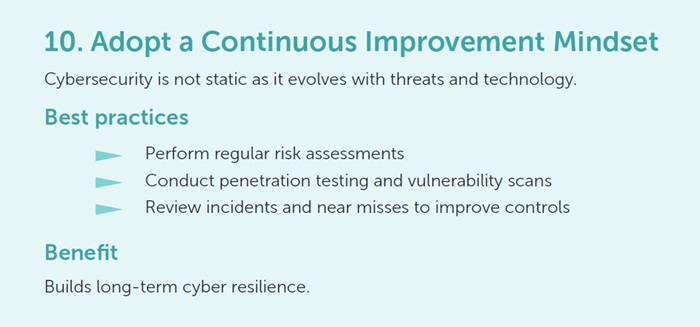
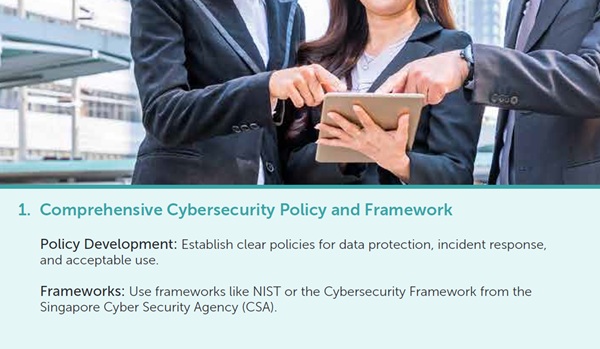
As cyber threats continue to grow in frequency and sophistication, securing systems is no longer optional, it is essential for business continuity, trust, and compliance. Strong cybersecurity practices reduce risk, limit damage during incidents, and help organisations operate with confidence in an increasingly digital environment.
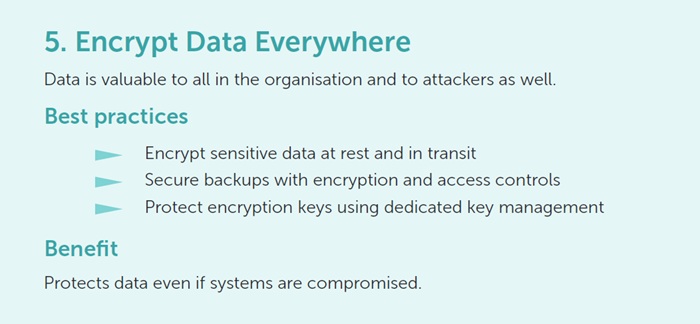
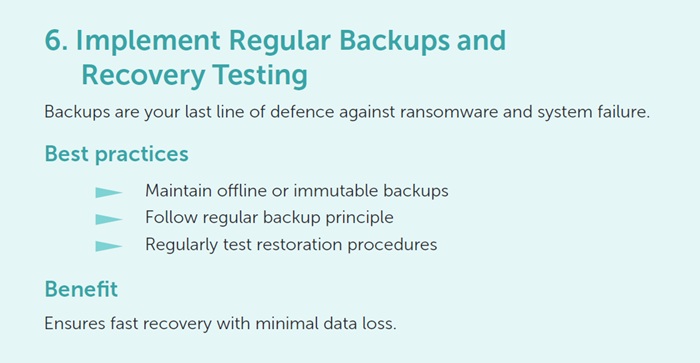
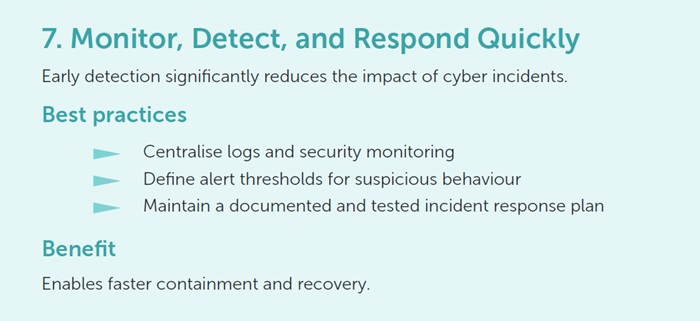
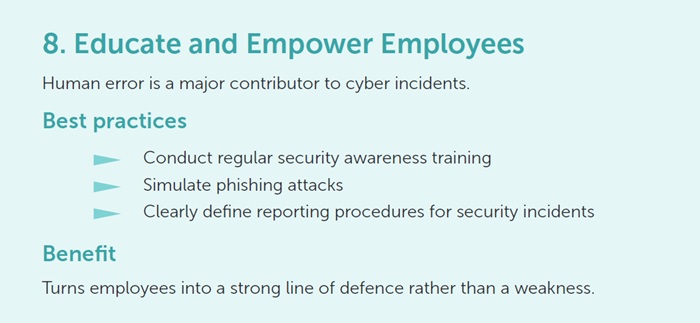
Some of the best cyber practices that should be adopted to protect systems and defend against cybersecurity risks.
Meticulous practical approaches to tackling these cybersecurity risks are essential to keep corporation systems safe. Practicing safe and secure measures will strengthen internal systems and will allow companies to be less susceptible to future occurrences of such threats.
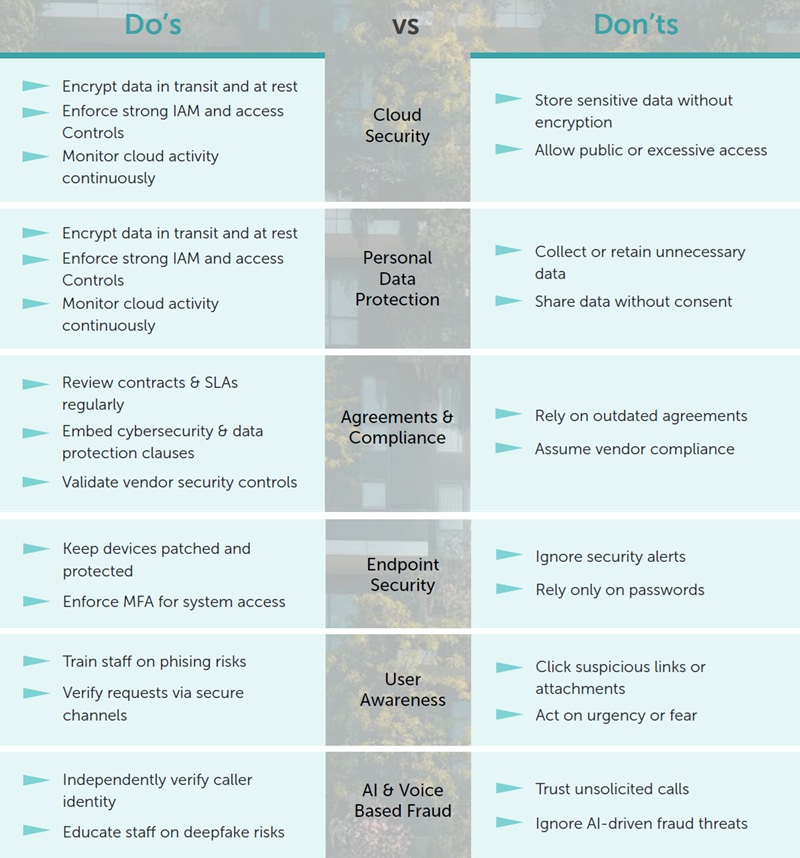
Through the forementioned practices, it is important that corporations secure and protect key aspects such as:
- Information Assets – Use encryption to protect sensitive business data.
- External Stakeholders – Ensure secure communication channels with partners and clients.
- AI Programs – Protect AI systems from tampering and data poisoning attacks.
- Cloud Systems – Implement strong access controls and encryption for cloud data.
Identifying the Threats
To prevent cyberattacks from occurring, staff within the corporations can take precautionary measures to prevent the threats before they happen.
- Unusual Network Traffic – Look for sudden spikes in traffc or data transfers to unfamiliar locations, which could indicate DDoS attacks or data exfiltration.
- Phishing & Social Engineering – Be aware of suspicious emails or messages with urgent requests, links, or attachments. Phishing often precedes larger breaches.
- Unfamiliar Logins – Monitor for logins from unusual locations or devices, particularly from foreign IP addresses or at odd hours. Use geolocation monitoring.
- Failed Login Attempts – Repeated failed logins, especially for privileged accounts, can signal brute force attacks. Implement multi-factor authentication (MFA) for added security.
- Unauthorized Software or Changes – Watch for unapproved software installations or sudden configuration changes, which may indicate malware or insider threats.
- System Slowdowns – Performance issues or crashes may signal malware, ransomware, or crypto-mining activities. Investigate unexplained resource use.
- Data Access Irregularities – Track unusual access to sensitive data, especially by employees or systems not usually involved with that data. Use Data Loss Prevention (DLP) tools.
- Vendor or Third-Party Risks – Regularly assess your supply chain security. A breach at a vendor can compromise your systems. Ensure vendors follow strong cybersecurity practices.
- Frequent Security Alerts – Don’t ignore repeated alerts from security software or tools. They may indicate an ongoing or imminent attack. Review logs regularly.
- Anomalies in Privilege Use – Monitor for unusual admin activities, such as privilege escalation or access to restricted systems without a valid reason.
Top Cybersecurity Dos and Don’ts
In order to effectively ensure the cybersecurity measures are capable of properly preventing cyberattacks from occurring, proper practice of the precautionary measures are to be observed to minimise potential loopholes in its defences.
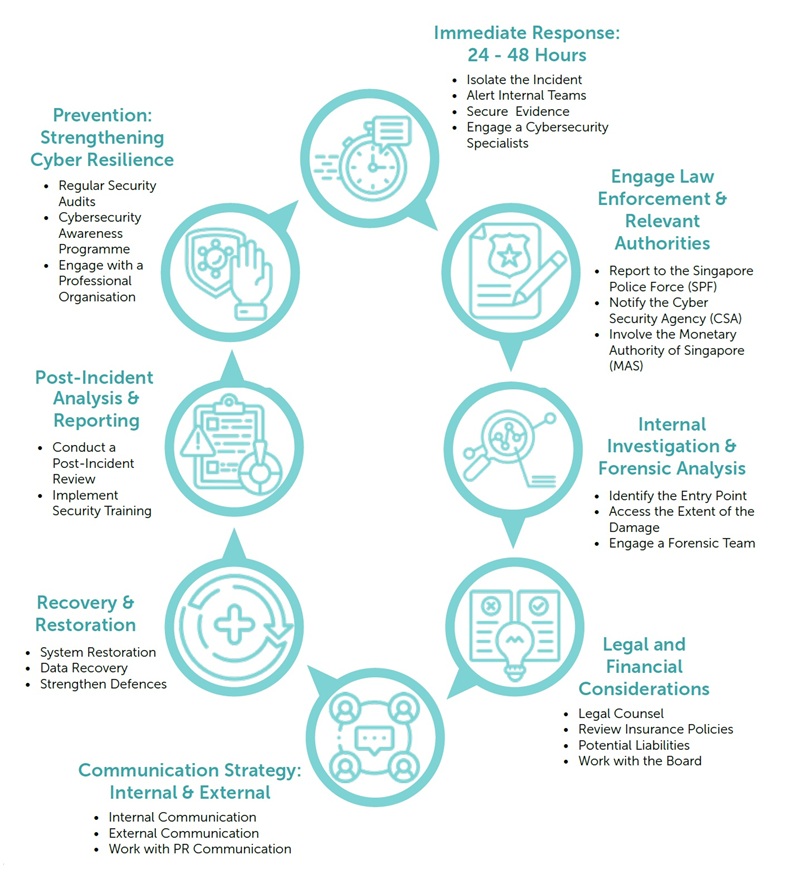
Example of Singapore’s Cyber Fraud Handling Process
Cyber Fraud – How is it dangerous?
Cyber Fraud is one of the most well-known cyber threats in the world of cybersecurity and one that may cause significant risks to a company. Through deceptions or theft via the internet, Cyber Frauds can lead an organisation to financial, reputational and operational risks.
In the case for Singapore, being a financial hub, it is highly exposed to cyber threats. In order to counter these attacks, policies such as the PDPA and Cybersecurity Act 2018 have been put in place in order to govern the occurrence of such threats.
View the full article in PDF here.
CONTACT US
CLA Global TS Business Advisors – Data Governance
 |
Pamela Chen Director, Head of Risk Advisory Data Governance, Sustainability & Climate Change pamelachen@sg.cla-ts.com |
 |
Maria Teo Director, Risk Advisory Data Governance, Sustainability & Climate Change mariateo@sg.cla-ts.com |
CLA Global Indus Value Consulting Business Advisors
 |
Kartik Radia CEO kartik.radia@claivc.com |
 |
Vikas Kumta Director, Cyber Security vikas.kumta@claivc.com |
 |
Xavier Sahaya CISO xavier.sahaya@claivc.com |